Evade firewalls and captive portals
When connecting to public WiFi networks, such as those provided in airports or hotels you are limited to a specific time period and your access might be limited to specific sites only. At first sight there’s no way around this because the connection limitations will not allow you to do much and hacking it isn’t advised either right?
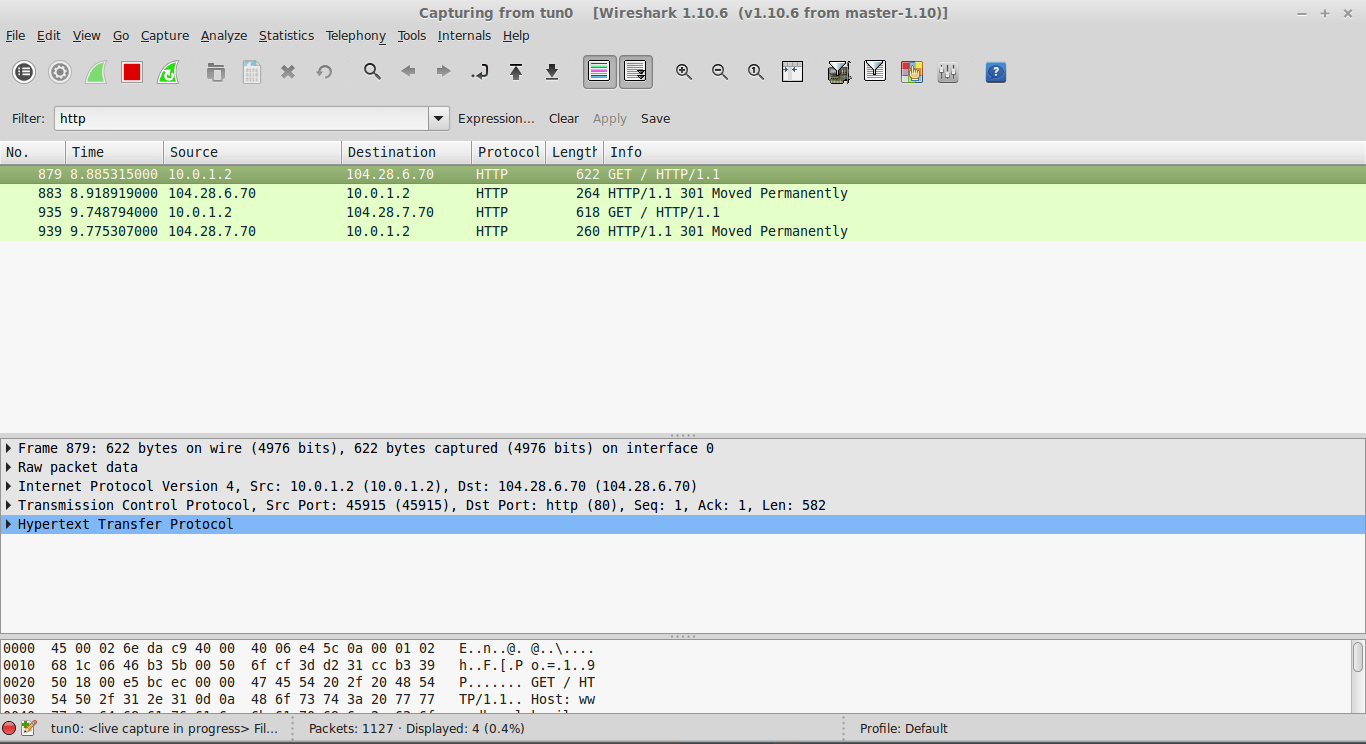
Well there is actually a way around this that does not imply hacking the captive portal and/or it’s firewall. To use the internet without issues from behind any captive portal or firewall you need to tunnel your traffic via ICMP.
You’re probably asking yourself how, well here’s a tool that I found on Github and which makes this possible: ICMPTunnel.
ICMPTunnel works by encapsulating your IP traffic in ICMP echo packets and sending them to your own proxy server. The proxy server decapsulates the packet and forwards the IP traffic. The incoming IP packets which are destined for the client are again encapsulated in ICMP reply packets and sent back to the client. The IP traffic is sent in the ‘data’ field of ICMP packets.
So basically the client machine uses only the ICMP protocol to communicate with the proxy server. Applications running on the client machine are oblivious to this fact and work seamlessly.
Pretty interesting right? All you need to make this work is to follow the installation instructions on the Github page and give it a go.