/usr/ Archive
Homelab enthusiasts like me debate the worst mistakes they’ve made along their journey so far. Windows users have been a target for ongoing attacks originating from Russian APTs and it seems that the situation is so dire that Microsoft had to issue a warning On the FreeBSD Foundation website you can find a case study
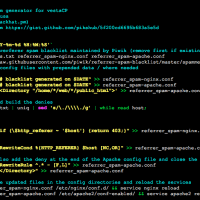
One of the nastiest problems when it comes to webserver resource and bandwidth usage is represented by the bad referrers which associate with a series of artificial queries from various hostnames that spam the crap out of the webserver and statistical logs. Because the accuracy of the statistical traffic reports is highly influenced by such
One of the most recent challenges I came across lately was to block malicious bots, harvesters and crawlers or other similar user-agents that should not access my data in Nginx. I already had such a system in place for Apache as I’m running all public websites with Apache, but since I have Nginx as reverse
I truly hate content lockers that have you do something in order to be able to access a page just so that those providing the stuff you’re accessing can build up email lists to spam the crap out of them or get more likes/shares on social media sites. A large volume of the content provided
Someone asked on r/Linuxadmin about setting up Let’s Encrypt certificates on the vestaCP admin panel and because I sought a solution for this before and also increased the security of my vestaCP panel by doing additional tweaks I’ve decided to write this article in order to help out all of you that run vestaCP and