[Tutorial] Install OpenVAS on Debian 9 (Stretch) – Updated
NOTE: This is an updated tutorial as the initial version contained a series of errors and required some additions.
Since Debian 9 (Stretch) has recently been officially released under the STABLE tag we might as well adopt it and use it further for our projects right?
Yesterday I checked my very long “to do” list and found installing and testing out OpenVAS amongst the thinks that were sitting there for a while so I decided to give it a try.
I checked the OpenVAS website and as you’d probably imagined already there weren’t any packages available for Debian 9. In fact there weren’t packages available for Debian 8 either or any other Debian versions as besides the native Kali Linux version, ports only exist for Fedora/CentOS/RHEL and of course Ubuntu.
But enough talking, let’s get down to business. First of all you need a bare minimum Debian 9 install and once you have it ready and available via SSH you should insure that the system is up to date by running then begin installing stuff:
apt update && apt upgrade && apt dist-upgrade
If you have an older image just as I have, once the upgrades are completed (if any) you should reboot the system to insure that you have the latest kernel running:
apt install -y build-essential cmake bison flex libpcap-dev pkg-config libglib2.0-dev libgpgme11-dev uuid-dev sqlfairy xmltoman doxygen libssh-dev libksba-dev libldap2-dev libsqlite3-dev libmicrohttpd-dev libxml2-dev libxslt1-dev xsltproc clang rsync rpm nsis alien sqlite3 libhiredis-dev libgcrypt11-dev libgnutls28-dev redis-server texlive-latex-base texlive-latex-recommended linux-headers-$(uname -r) python python-pip mingw-w64 heimdal-multidev libpopt-dev libglib2.0-dev gnutls-bin certbot nmap ufw
This will install most of the stuff required to compile and run OpenVAS.
Now it’s time to get down to business and download the sources for OpenVAS 9, it’s extras and the compatible scanner wrappers. The download page for all this stuff can be found here.
Download everything:
wget http://wald.intevation.org/frs/download.php/2420/openvas-libraries-9.0.1.tar.gz wget http://wald.intevation.org/frs/download.php/2423/openvas-scanner-5.1.1.tar.gz wget http://wald.intevation.org/frs/download.php/2448/openvas-manager-7.0.2.tar.gz wget http://wald.intevation.org/frs/download.php/2429/greenbone-security-assistant-7.0.2.tar.gz wget http://wald.intevation.org/frs/download.php/2397/openvas-cli-1.4.5.tar.gz wget http://wald.intevation.org/frs/download.php/2377/openvas-smb-1.0.2.tar.gz wget http://wald.intevation.org/frs/download.php/2401/ospd-1.2.0.tar.gz wget http://wald.intevation.org/frs/download.php/2405/ospd-debsecan-1.2b1.tar.gz wget http://wald.intevation.org/frs/download.php/2218/ospd-nmap-1.0b1.tar.gz
Once you’re done insure that you have all the files and start extracting them:
-rw-r--r-- 1 root root 3225150 Jul 17 08:06 greenbone-security-assistant-7.0.2.tar.gz -rw-r--r-- 1 root root 113958 Jul 17 08:06 openvas-cli-1.4.5.tar.gz -rw-r--r-- 1 root root 649251 Jul 17 08:05 openvas-libraries-9.0.1.tar.gz -rw-r--r-- 1 root root 2196486 Jul 17 08:06 openvas-manager-7.0.2.tar.gz -rw-r--r-- 1 root root 256812 Jul 17 08:06 openvas-scanner-5.1.1.tar.gz -rw-r--r-- 1 root root 1097616 Jul 17 08:07 openvas-smb-1.0.2.tar.gz -rw-r--r-- 1 root root 50840 Jul 17 08:07 ospd-1.2.0.tar.gz -rw-r--r-- 1 root root 13735 Jul 17 08:07 ospd-debsecan-1.2b1.tar.gz -rw-r--r-- 1 root root 12073 Jul 17 08:07 ospd-nmap-1.0b1.tar.gz
You can extract them all in bulk with a command string hack (spares you the time of doing each archive manually)
for i in $(ls *.tar.gz); do tar zxvf $i; done
Now that all are extracted we must start to compile and install each of them.
To do that we need to go into each of the following directories (the order is mandatory for successful compilation of each component):
- openvas-libraries-9.0.1
- openvas-manager-7.0.2
- openvas-scanner-5.1.1
- openvas-cli-1.4.5
- greenbone-security-assistant-7.0.2
and run the commands below:
cmake . && make && make doc && make install
You can either run them separately one by one or as a single line.
NOTE: Each directory has a file called INSTALL where you will find instructions on how to install each pack. However, the instructions are for Debian 8 (Jessie) and they assume installing the needed libraries and dependencies one by one instead of installing them all in bulk at once as I’m explaining in this tutorial. Therefore, since the idea behind this tutorial is to work smarter not harder I will be trimming the steps as much as possible.
I assume that by now you noticed that I did not include the openvas-smb-1.0.2 in the list of directories. That’s because the compilation of winexe fails on Debian 9 and I haven’t found a way around it just yet. Since the OpenVAS suite works without the SMB plugin I will skip it for the time being and will update this tutorial with the workaround as soon as I find it.
Now, for the remaining extras we go into each of the following directories (the order is mandatory just as well):
- ospd-1.2.0
- ospd-debsecan-1.2b1
- ospd-nmap-1.0b1
and run this command line to build and install the scripts:
python setup.py build && python setup.py install
As soon as you’ve completed the installation (and didn’t get any errors while doing so) we need to configure Redis to work with the OpenVAS scanner daemon so we edit the /etc/redis/redis.conf file and set the port to 0 in order to make Redis listen on an Unix socket instead:
port 0
Once the port is set we also have to uncomment the following lines in order to define the socket file and it’s permissions:
unixsocket /tmp/redis.sock unixsocketperm 700
Once this is all set we need to restart the Redis server:
service redis-server restart
Now the trouble is that systemd forces Redis to open the socket using temporary path while OpenVAS (and I think this is hardcoded) tries to look for the socket in /tmp/redis.sock. To solve this issue I came up with this dirty hack of creating a symlink:
ln -s /tmp/systemd-private-*-redis-server.service-*/tmp/redis.sock /tmp/redis.sock
(Update) Before running the OpenVAS scanner daemon we must insure that the libraries compiled earlier are loaded so we run:
ldconfig
Once this has been setup we can start the OpenVAS server with this command:
openvassd
And update all the databases with these commands to download the databases, extract them and rebuild the caches:
greenbone-nvt-sync && greenbone-scapdata-sync && greenbone-certdata-sync openvasmd --progress --rebuild
NOTE: This will take a while, depending on the server resources and internet connection speed so it would be a good time to take a break while the task runs.
Once the database sync is completed we’ll move onto setting up the SSL certificate as the Greenbone Security Assistant daemon starts over HTTPS:
openvas-manage-certs -a
This command will automatically create a self-signed certificate and install it. Once the certificate is installed we can proceed with starting up the manager, the scanner module and Greenbone Security Assistant daemon by executing their binaries:
openvassd openvasmd gsad
openvasmd --create-user=blackhat --role=Admin
- The databases need to be updated frequently;
- If the server reboots the daemons stop and don’t start by themselves;
Fortunately we have a solution for them as well.
First and foremost let’s create a database update script as the /usr/local/sbin/openvas-db-update file. Edit this file with your favorite text editor and thrown in the following lines:
#!/bin/bash echo "Updating OpenVAS Databases" greenbone-nvt-sync greenbone-scapdata-sync greenbone-certdata-sync
Save the file and make it executable using chmod +x /usr/local/sbin/openvas-db-update.
Next because we want this to run daily (I think that’s frequent enough) we edit the cron using crontab -e and add the following lines to the file:
# OpenVAS Daily Database Updates 0 0 * * * /usr/local/sbin/openvas-db-update
This will run the database update script each day at midnight.
With one problem out of our way let’s move onto creating the startup scripts so we’ll create three files and will make them executable with chmod +x as follows:
- OpenVAS Manager: /etc/systemd/system/openvas-manager.service
- OpenVAS Scanner: /etc/systemd/system/openvas-scanner.service
- Greenbone Security Assistant: /etc/systemd/system/greenbone-security-assistant.service
The contents of each startup script is listed below:
openvas-manager.service:
[Unit] Description=Open Vulnerability Assessment System Manager Daemon Documentation=man:openvasmd(8) http://www.openvas.org/ Wants=openvas-scanner.service [Service] Type=forking PIDFile=/usr/local/var/run/openvasmd.pid ExecStart=/usr/local/sbin/openvasmd --database=/usr/local/var/lib/openvas/mgr/tasks.db ExecReload=/bin/kill -HUP $MAINPID # Kill the main process with SIGTERM and after TimeoutStopSec (defaults to 1m30) kill remaining processes with SIGKILL KillMode=mixed [Install] WantedBy=multi-user.target
openvas-scanner.service:
[Unit] Description=Open Vulnerability Assessment System Scanner Daemon Documentation=man:openvassd(8) http://www.openvas.org/ After=redis-server.service Requires=redis-server.service [Install] WantedBy=multi-user.target [Service] Type=forking PIDFile=/usr/local/var/run/openvassd.pid ExecStart=/usr/local/sbin/openvassd ExecReload=/bin/kill -HUP $MAINPID # Kill the main process with SIGTERM and after TimeoutStopSec (defaults to 1m30) kill remaining processes with SIGKILL KillMode=mixed
greenbone-security-assistant.service:
[Unit] Description=Greenbone Security Assistant Documentation=man:gsad(8) http://www.openvas.org/ Wants=openvas-manager.service [Service] Type=simple PIDFile=/usr/local/var/run/gsad.pid ExecStart=/usr/local/sbin/gsad --foreground [Install] WantedBy=multi-user.target
After we’ve completed the creation of the startup scripts and we’ve made them executable we should test the OpenVAS installation and we can do that by pulling the test script and running it:
cd ~ && wget --no-check-certificate https://svn.wald.intevation.org/svn/openvas/trunk/tools/openvas-check-setup chmod +x openvas-check-setup ./openvas-check-setup --v9
If all goes well you should see an output with all the components being checked and warnings being displayed for things that need tweaking. If you did something wrong throughout the process the setup check script will exit and recommend a fix for the problem found.
Now if the setup check script does not find any errors then we will have to setup the services to start automatically at reboot and we can do that by using systemctl:
systemctl enable openvas-manager.service && systemctl enable openvas-scanner.service && systemctl enable greenbone-security-assistant.service
The next step we should take would be to try and reboot the server in order to make sure that the service startup scripts work correctly. We could do that without rebooting by killing the processes and doing a manual start, yet in my opinion rebooting is much more accurate which is why I recommend it.
However, before rebooting we still have one thing to fix. Remember that previously the redis.sock socket file was created under a temporary path which means that when the server gets rebooted the temporary file is gone and so is the symlink. In this case upon reboot the OpenVAS scanner daemon will not be able to start without the correct Redis socket file which should be /tmp/redis.sock, but because the SystemD generates a temporary path and the symlink bandaid I used earlier does not get applied upon reboot we’ll have to alter the configuration a bit to make it work as it should.
To make it happen we’ll have to edit the /etc/systemd/system/redis.service file and change the PrivateTmp value from “yes” to “no”:
PrivateTmp=no
Then a few lines underneath the one referenced above, right after the line that says: ReadWriteDirectories=-/var/run/redis; we’ll add another one to allow it to write the socket file in /tmp:
ReadWriteDirectories=-/tmp
After you save the file you should reboot and allow the system a couple of minutes to start everything as on VPS platforms the OpenVAS scanner needs a couple of minutes to initialize the databases.
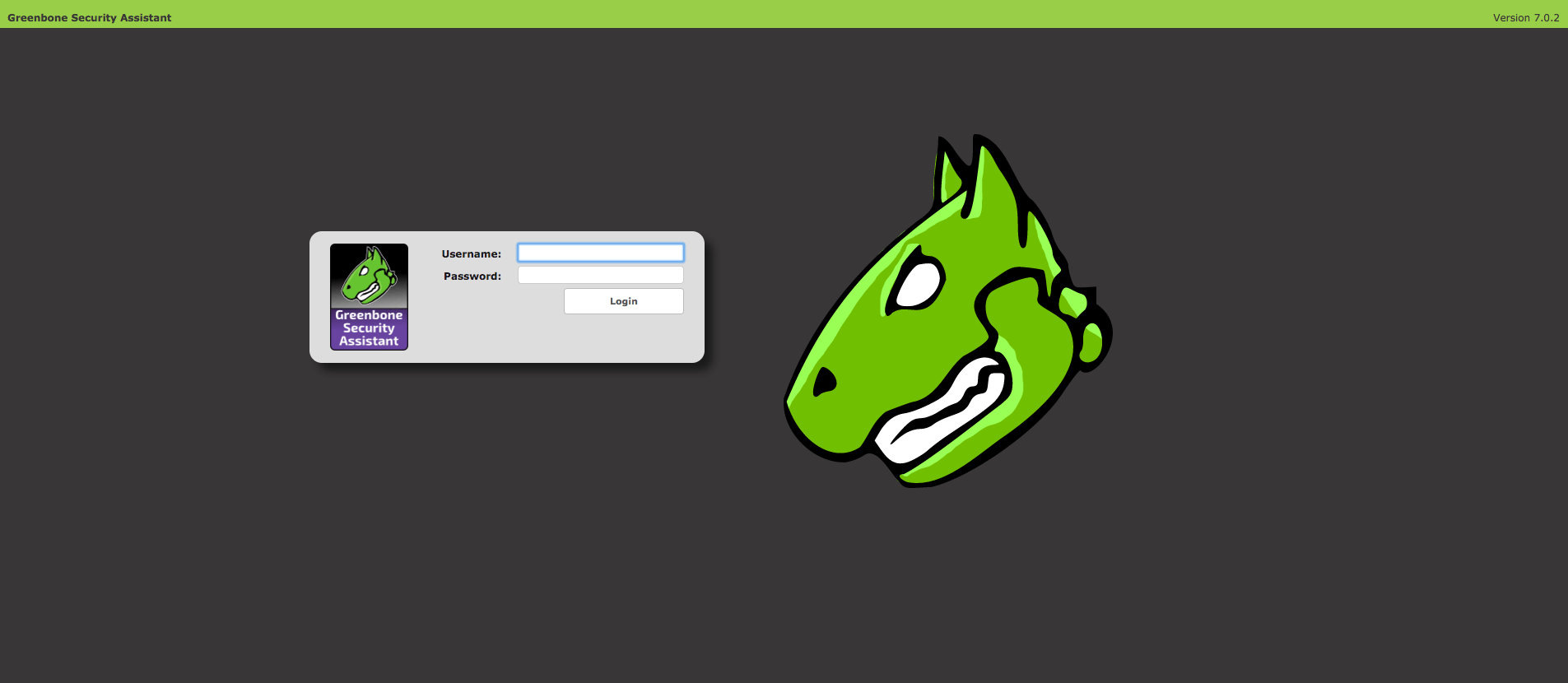
Then once the system has booted up you should be able to access the Greenbone Security Assistant via the browser and use it as you see fit.
RESOURCES:
- Chris Bradford’s tutorial for OpenVAS on Debian 8 (Jessie);
- OpenVAS’ source installation page;
TO DO:
- Fix the SMB module compilation;
Setup Greenbone Security Assistant using Let’s Encrypt SSL certificates;done! – tutorial coming next.

![[Tutorial] Pritunl with Nginx reverse proxy & Let’s Encrypt](https://www.blackhat.pm/wp-content/themes/sensational/images/relthumb.png)